Applications to spy on Instagram
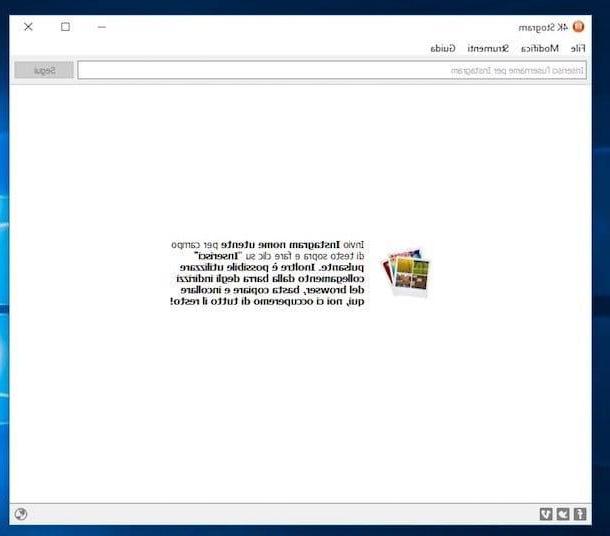
There are several applications that allow you to spy on instagram at a distance. I'm referring to apps like Cerberus, which was born as an anti-theft solution but can also be used for other purposes, including spying on Instagram. There are also applications, such as Story Saver for Instagram (per Android) e Story Reposter (for iOS), which allow you to spy on Instagram stories without being seen - let me explain them to you in detail.
Cerberus
Cerberus is a very famous anti-theft application, which allows you to control a smartphone from a distance. In addition, it allows you to capture screenshots remotely, a function through which it is theoretically possible to spy on Instagram. Available for phones only Android, the app is a free trial for the first 7 days, during which you have access to all premium features. After the trial period, in order to continue using the app, you must purchase the full version at a cost of 5 euros.
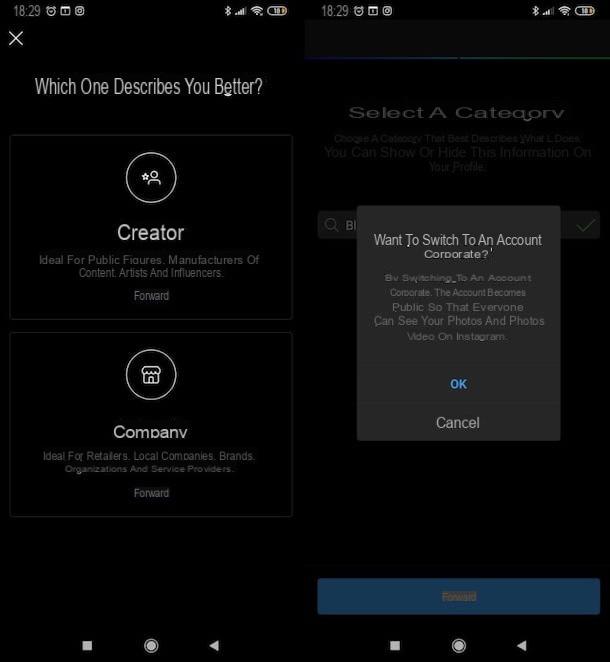
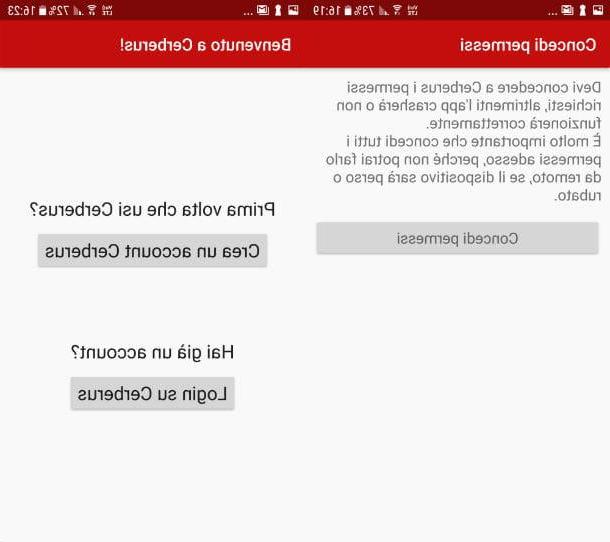
If you intend to try Cerberus, connect to the official application page on the Play Store using the phone of the person you want to check on Instagram and tap the button Install to start the installation. When the download is complete, open the app and, in the screens that open later, tap the button Grant permissions seven consecutive times. Now, hit the command Change system settings and, in the new screen, put the check mark next to the item Allow changing settings.
Once the permissions have been granted, go back by pressing the button Home of your smartphone and reopen the application. On the screen of Welcome, tap on the item Create a Cerberus account, then fill in the fields Choose a username, Scegli a password, Confirm Password, Please enter your email address e Confirm Email Address and finish the creation of the profile by pressing the button Create account.
In the new screen that appears, Cerberus Terms and Conditions, if you intend to accept the contractual conditions of the app, tap on the item Create account. Now, do it three swipes from right to left and, if you have a rooted phone, in the screen that opens, tap on the command Conceded. Remember that the Cerberus application and other spy apps, to work at their best, must be installed on a phone that has obtained root permissions.

Now, if you want to spy on the Instagram profile of the person who owns the phone on which you have installed Cerberus, connected to the Cerberus web panel from your computer, select the item Login (top right), fill in the fields Username e Password with the credentials used during registration and, to complete access, click on the button Login.
When you have entered the main screen of the Cerberus management panel, click on the button down arrow placed next to the item Start localization and, in the drop-down menu that opens, scroll down until you select the item Take screenshots. Alternatively, you can also select commands Video capture e Screen recording capture, so as to receive in real time the activity carried out at that precise moment by the unsuspecting victim.
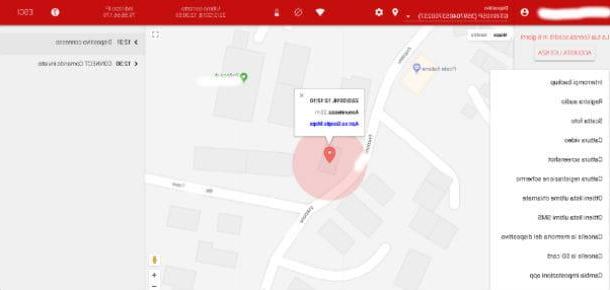
A concrete example: the person you want to spy on is writing a comment on Instagram, while you have just sent the command to the Cerberus app to take a screenshot. After a few seconds, you will receive the photo of the smartphone screen on which you downloaded the application, where you can read both the comment and the recipient of the latter.
Screenshots, videos and screen recordings can be viewed as attached files within the emails that the spy application automatically sends to the email address with which you registered for the service.
If you are interested in learning more about the subject and / or want advice on other spy apps that can be used for Instagram, I recommend reading my guide on how to spy on a mobile phone remotely.
Story Saver for Instagram
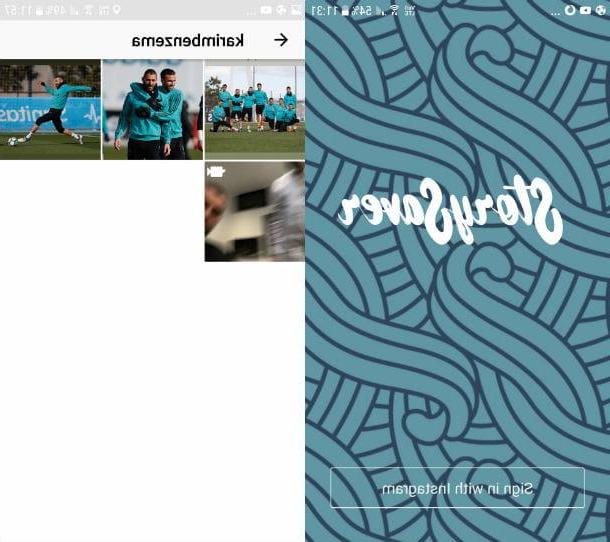
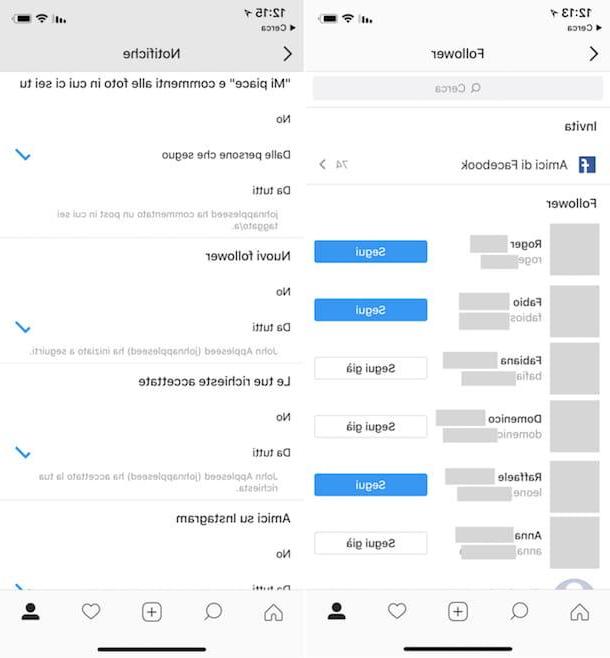
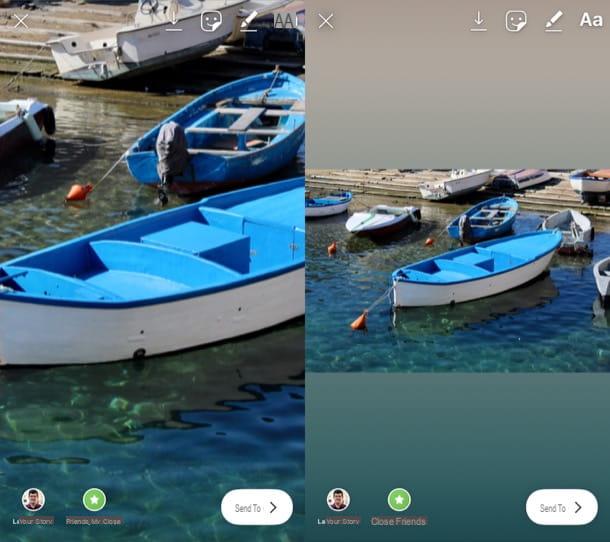
The free application Story Saver for Instagram for Android allows you to download the stories of Instagram users without them noticing: an excellent solution to "spy" on other people's profiles! The downloaded files can be stored in the phone memory, shared on Facebook and Twitter or alternatively, used for a repost on Instagram (functions which, however, should not be needed at this time).
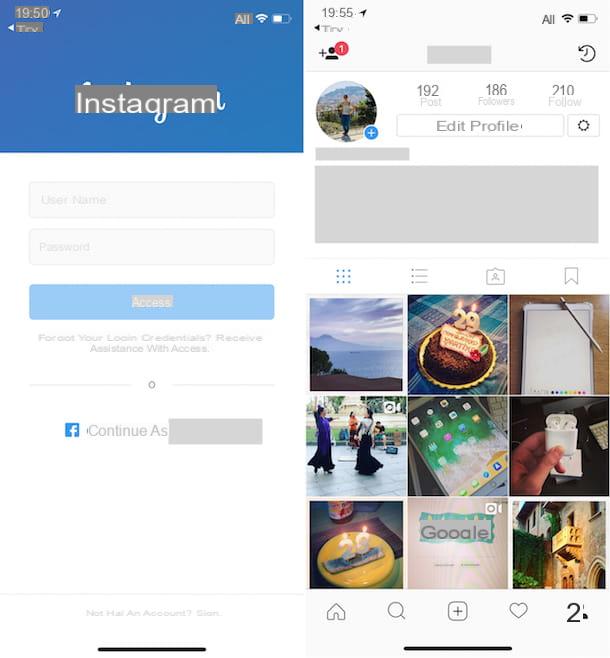
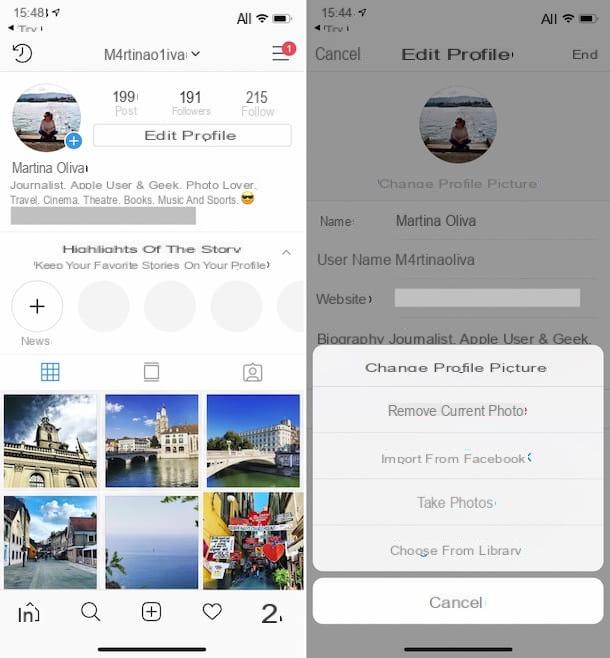
After installing and starting Story Saver, tap on the button Sign in with Instagram to connect it to your Instagram account. Then complete the operation by filling in the fields Username e Password, then tap on the button Log in. Now, on the main screen of Story Saver for Instagram, you can see the users who have recently made an Instagram story. So tap onuser icon you intend to monitor, select theimage or video you want to save and, in the screen that opens, presses on the option Save.
To view the content just saved, go back to the main application screen, press the button ☰ and, in the drop-down menu that opens, select the item History. On the new screen, you can find the photo or video you previously saved. The file is also saved in the phone's internal memory: you can find it in the Gallery, in the path Album > Story saver.
Story Reposter
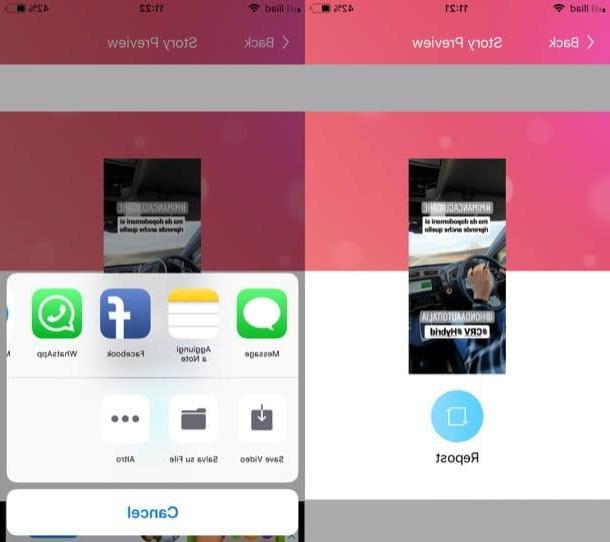
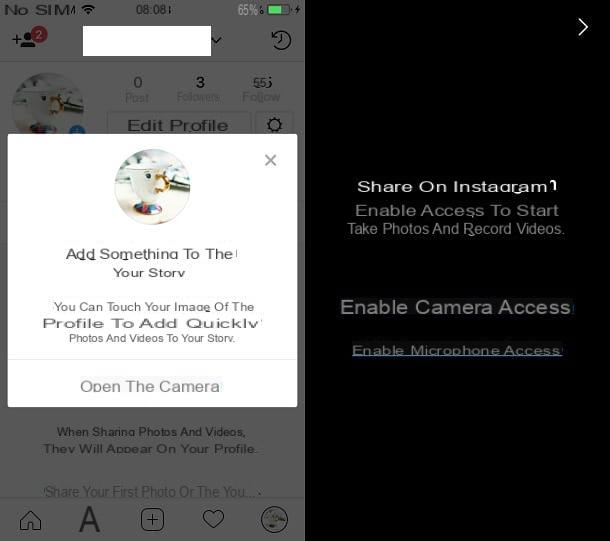
If you own a iPhone, an application that can do for you is called Story Reposter. If you have never heard of it, this is a free app that was designed to allow reposting of Stories, but which you can use to watch this content if necessary without the respective creators knowing. I point out, however, that from the tests I conducted, the app is not able to view the Stories made by private accounts.
After installing and starting Story Reposter, scroll through the information sheets that show you how it works, press the button Close and grant her permission to access the camera roll of your "iPhone by". Next, search for the name of the user you want to "check" in the search bar Type the name of the Instagram user and presses the button SEARCH.
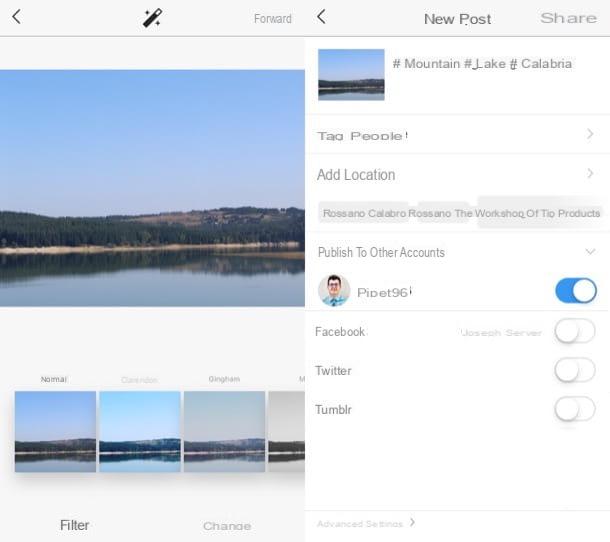
Identify, therefore, the username that corresponds to the account of your interest, presses on it and tap the button Video/Photo posted [N] minutes/hours ago which is located in correspondence with the content you intend to view. After seeing the preview, press the button repost, select the voice More from the menu that opens and then tap the button Save Photo/Save Video to download the content to your device.
Techniques to spy on Instagram
In addition to spy apps, there are other ways to spy on a user on Instagram. One of these is theSOCIAL ENGINEERING, also known as social engineering. This is a technique that does not require the use of any app, but is based on the inexperience and inattention of the intended victim. Let me talk about it in more detail, along with other possible "weapons" available to cybercriminals.
Social engineering

Typically, the individual engaging in social engineering is aided by an accomplice, whose role is to distract the potential victim.
The cybercriminal, taking advantage of the victim's naivety, finds a way to get hold of his device, for example by pretending to have to make an urgent call and not to be in possession of a mobile phone. At that point, it can steal a whole series of sensitive data, such as Instagram account credentials and the activities carried out by the user on the latter. Furthermore, the attacker can install spy apps and in this way start a monitoring of the user's activities remotely.
If you don't have a lot of experience using smartphones or are just plain careless, you can be the next victim of social engineering. If you want to avoid getting trapped by a cybercriminal, take better care of your phone. Above all, never lend it to people you don't know or to individuals you don't trust enough. As a wise saying goes: trusting is good, not trusting is better!
Keylogger

Hackers don't stop at social engineering if they intend to spy on Instagram, but they can use software called keylogger, thanks to which they can easily monitor the activity of the unsuspecting user. Keyloggers are installed on a PC or smartphone and record every word that is typed with the keyboard.
These are very dangerous software, as they violate the victim's privacy heavily and steal any password typed, obviously also that of Instagram. There are more complex keyloggers that allow the hacker to act remotely, while others are used for home use.
One of the easiest to use PC keyloggers, really affordable for everyone, is called Home KeyLogger: if you are interested in knowing how it works, I invite you to read my post on how to spy on a PC with a keylogger.
Theft of passwords stored in the browser

Another technique that hackers can use to spy on Instagram is to log into passwords stored in browser databases, where they could also find the keyword used to login on Instagram.
Many allow Internet browsers to memorize their login credentials to a website, without thinking in the slightest about the risk associated with this practice. If a hacker were to get hold of previously saved passwords from browsers, the first thing he or she would probably do would be to hack all the sites they can enter undisturbed. For further information, I invite you to read my tutorial on how to hack an Instagram profile.
How not to be spied on Instagram
After learning how to spy on Instagram, it is good to see what are the best precautions to take to avoid falling into the trap of cybercriminals.
- Use a secure password: Using a password that is extremely difficult to guess is the first step to take if you want to avert the risk of being spied on on Instagram. Therefore, passwords that are too trivial, for example the sequence of numbers, are banned 123456789 or your own date of birth. To be secure enough, a password should have one length from 15 to 20 characters. Also, it is recommended to use uppercase and lowercase letters, numbers and special characters within the same keyword. If you need advice on how to create a secure password, check out my tutorial on the subject.
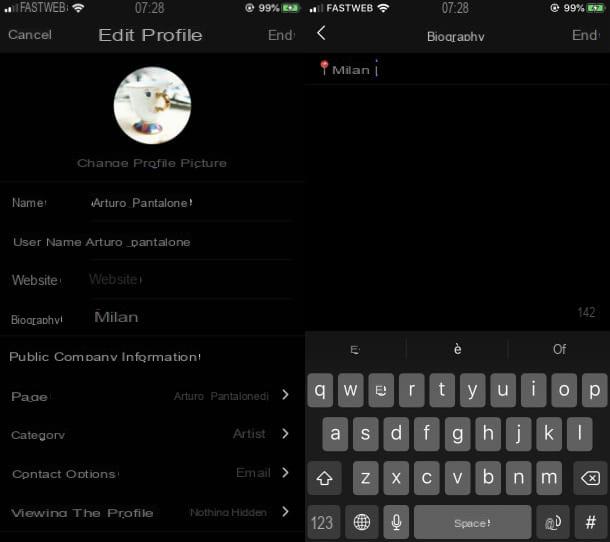
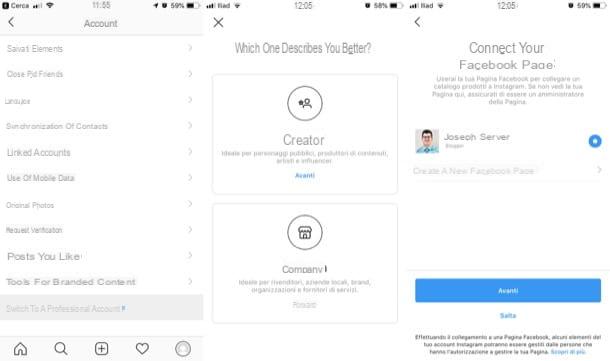
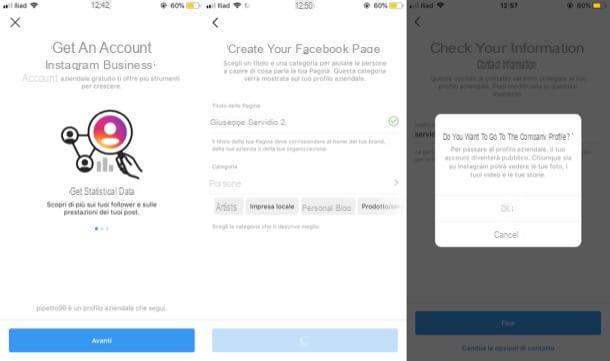
- Enable two-factor authentication: Sometimes, even a password that is believed to be secure can be discovered. For this reason, it is advisable to activate thetwo-factor authentication on Instagram to increase the security level of your account. Enabling two-factor authentication is an operation that takes a few seconds. Then open Instagram, fai tap sull 'three dots icon (top right) and, in the screen that opens, select the item Two-factor authentication. Now put the check mark next to the option Request security code and, in the new screen that opens, presses the button Active but I will complete the procedure.
- Use a secure PINBetter smartphone protection also comes with having a secure phone unlock PIN. The best solution is to have a 6-digit PIN or an unlock through the biometric sensor. Nowadays, many smartphones have the fingerprint reader. The most recent phones, on the other hand, are adopting facial recognition as an unlocking method.
- Don't lend your phone to strangers: it may seem trivial, superfluous advice, but it is not. There are still many people who make the mistake of lending the phone to complete strangers who, once in possession of the device, can put into practice the techniques mentioned in the previous chapter.
- Do not connect to public Wi-Fi networks: this is another trivial piece of advice, but one that is often overlooked. Public Wi-Fi networks are often exposed to cyber attacks aimed at sniffing data. If you are at the airport, in a shopping mall or in a public area that offers free Wi-Fi, use your data connection. Also, if you can, use a VPN like NordVPN (which I told you about in depth here) or Surfshark to encrypt connection data and protect you from malicious people and tracking activities by providers.
- Check for spy apps: Less complex spy apps are easily found on the phone where they were previously installed. If you have a smartphone Android, open the Settings and presses on the voice Application. On the new screen that appears, check that there are no apps other than the ones you downloaded. Another way to check that there are no spy apps on your phone is to check which apps have the administration permissions, without which a malicious app cannot work. Open the again Settings (the gear icon), tap on the item Lock screen and security and, in the screen that opens, tap on the option Other security settings. Finally, select the item Device administrators and, in the new screen that appears, check that there are no spy applications. If, unfortunately, you find one, remove the check mark next to the app. If, on the other hand, you have a iPhone, to check for any spy apps, open the Settings, tap on the item Generali and, in the screen that opens, select the item Free space iPhone. In the new screen, check all the apps installed on the "iPhone by": if you find a spy application, tap on it and, in the new screen, press the button Delete app. Then go to the menu Settings> General> VPN and find out if there are any suspicious VPNs configured in iOS (spy apps often use VPNs to spy on users' activities). To learn more, find out how to delete spy software from your mobile by reading my tutorial about it.